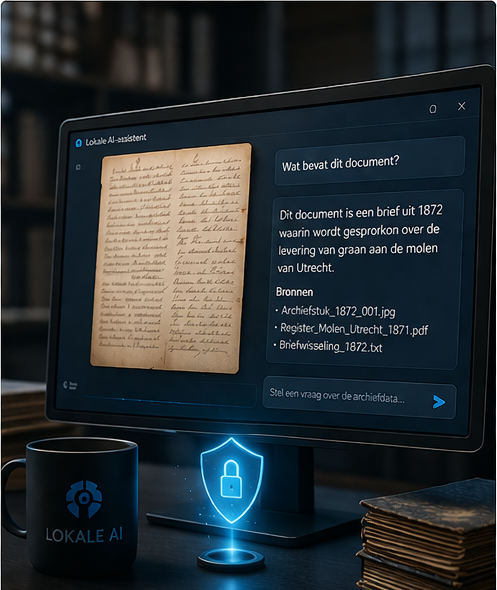
Archive digitisation with GDPR-aware setup
Even privacy-sensitive information often still needs to remain searchable, workable or transferable. That is why we look for a balanced approach in which accessibility and protection do not work against each other unnecessarily. The goal is not to make information unusable, but to decide carefully what may be visible to whom.